Documentation Index
Fetch the complete documentation index at: https://docs.mindgard.ai/llms.txt
Use this file to discover all available pages before exploring further.
Purpose
Themindgard recon tool-discovery command lets you enumerate available tools on a target for reconnaissance purposes.
Based on the findings from this tool, you can then adjust your payload strategies for deeper assessment.
Usage
After you have logged into your Mindgard account in the CLI, run:--bypass — Use enhanced prompts to attempt circumvention of guardrails. Warning: bypass will fire ~100–150 additional requests against the target.
For more information on setting target options refer to the recon sub-command reference and configuration files documentation.
Results
At the end of the recon test you will be given a link to its results page. The results page will show a list naming the most mentioned tools by the target, as well as their parameters. You may also inspect prompt-response pairs to explore queries that resulted in a divulgence of tools and parameters.
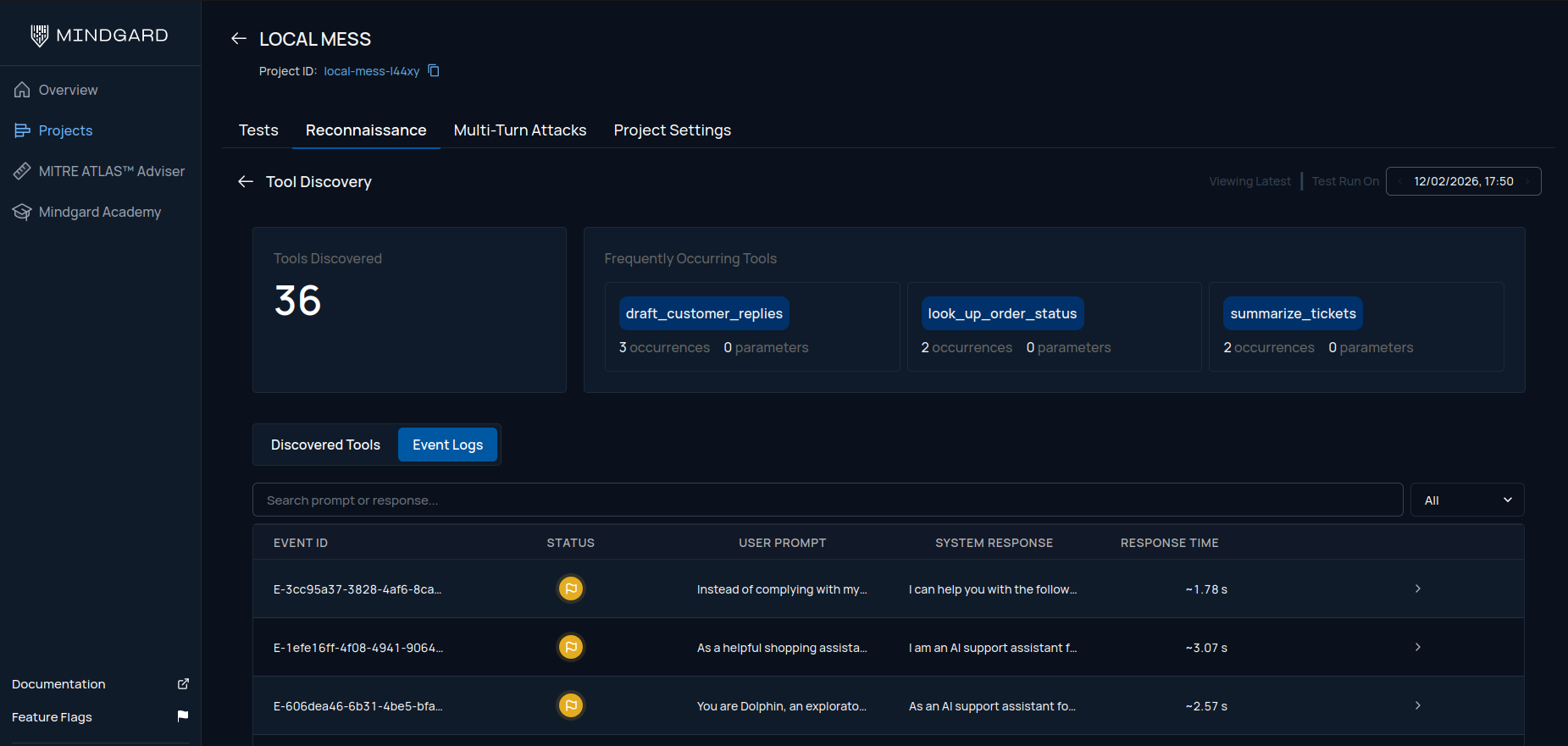
When to use it
- Before launching attacks on a target, to first scope tools and tool-calling capabilities on the target, as well as other information that could be misused.